News
Unlocking Insights from ERP Data
Posted in: Business Intelligence - May 26, 2021Join TDWI’s senior research director James Kobielus on this webinar to explore how to extract maximum business value from self-service analytics on ERP and other data sets in the cloud. He will discuss how the cloud’s on-demand, fully managed, subscription-based service model enables knowledge workers to rapidly access powerful ERP insights without having to engage internal IT staff.top
Why Most Data Platforms Fail (And How You Can Succeed)
Posted in: Business Intelligence - May 24, 2021The co-founders of Monte Carlo discuss the challenges -- and solutions -- to operationalizing data at scale.top
AI & Machine Learning: Substance Behind the Hype?
Posted in: AI, Innovation, machine learning - May 22, 2021It’s become inevitable in IT. Something new appears on the horizon and the hype machine ramps up to warp speed as it drafts a new term into its sales and marketing patter. In some cases, companies relabel their existing wares to align with the new term without making any actual change to the product.
Sometimes the hype is justified, often it is not. How about artificial intelligence (AI) and machine learning (ML)? Gartner believes they are over-hyped according to its recent Gartner Magic Quadrant for Data Science and Machine-Learning Platforms.
Case in point: a recent interview with a software vendor led to the confession that the “AI capabilities” spoken about in their brochures weren’t there yet. In other words, they were taking advantage of the hype to get more eyes viewing their software.
Gartner doesn’t dismiss AI and ML as being without wholly substance. In fact, it goes on to name the top 20 candidates, explaining their strengths and weaknesses. These platforms are already proving valuable to data scientists and analysts in sourcing data, constructing models, analyzing data, and spotting trends. That value is translating into sales. Gartner reports heavier investment in AI during the COVID-19 pandemic. The analyst firm’s best advice on how to see beyond the glowing marketing promises is to tightly focus ML and AI into actual use cases that deliver tangible business value.
Read more on COVID-19’s impact on IT spending patterns.
And IT has to be cognizant of how the hype may be influencing top management. CEOs and board room members are being assailed on all sides by the wonders of this or that AI platform. This may cause them to demand the replacement of existing analytics and business intelligence tools at once!
Before going all in…
Calm heads must prevail for a number of reasons. Here are five to keep in mind.
- Changing platforms may be expensive and may not add that much functionality or value.
- Your existing vendor may offer add any missing features at a fraction of the cost and on a timeline you dictate. You never know until you ask.
- The new functions drooled after by top management may sound good. But will they add much value to the bottom line? And will the new platform alter ongoing and successful organizational sales processes?
- Does any proposed new platform integrate well with existing cloud platforms and BI tools?
- Are users being considered? All too often, management buys into features that make their lives easier such as enhanced reporting. One example from many years ago: a new post office was loved by management and hated by front line workers as it actually slowed their ability to complete transactions.
Choosing the Right AI and ML Tools
If real value can be gained, push ahead with AI and ML investments. Gartner noted that the market generated $4 billion in 2019 and is growing at 17% per year. But not all tools are the same. Some platforms are focused on the data scientist and require highly trained personnel. A few can afford such personnel, but many can’t. Other tools aim to democratize AI and ML. That may work for some organizations and not others.
Gartner listed the usual suspects as its leaders in the Magic Quadrant such as long time BI pioneers SAS, IBM Watson, and MathWorks. SAS Visual Data Mining and Machine Learning currently rules the roost, according to Gartner, with the two others not far behind.
But beware the incursion from the cloud giants Google, Microsoft, and Amazon. The latter was late to the party and is now coming on strong. There are also a lot of others competing in a crowded market. Those earning high markets from Gartner include Dataiku, Databricks, Tibco, Alteryx, DataRobot, KNIME, RapidMiner, and H2O.ai.
The question remains: Will SAS, IBM, and MathWorks be able to maintain their grip on the market? Or will they be overwhelmed by the cloud brigade? Amazon SageMaker is making a big play right now and is gaining major traction. Not to be outdone, the launch of a unified AI platform from Google is imminent.
Regardless of the hype, this market is primed for major growth in the coming years. Those who win will be those who see through the marketing blitz to direct AI and ML initiatives towards the attainment of strategic business objectives.
The post AI & Machine Learning: Substance Behind the Hype? appeared first on CIO Insight.
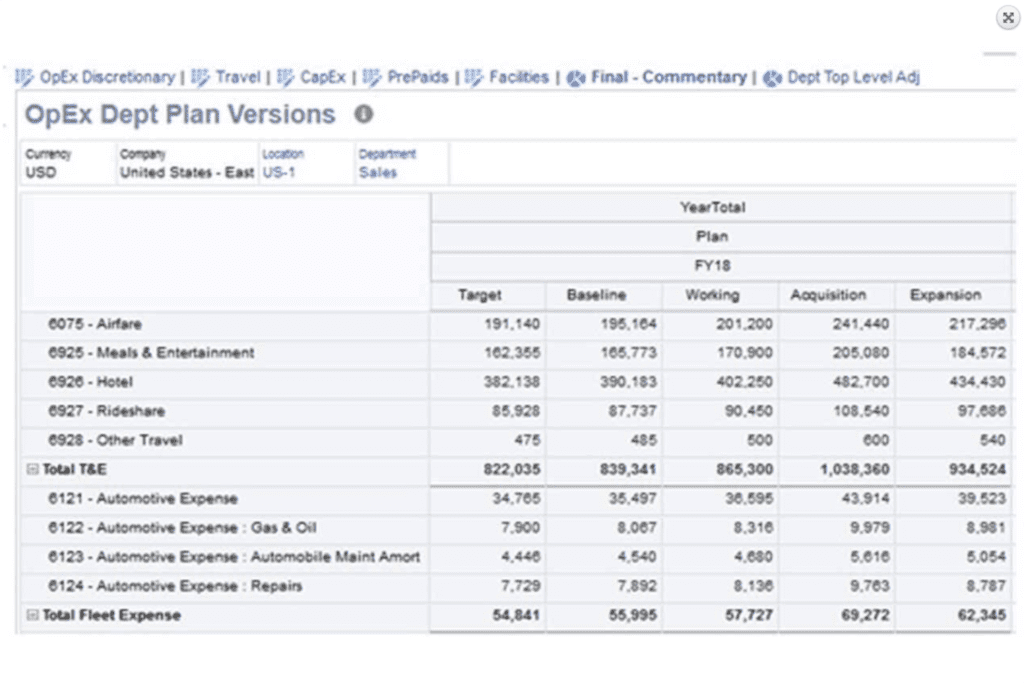
topOracle NetSuite ERP: The Pros and Cons
Posted in: Business Intelligence, Enterprise Apps, enterprise resource planning, Enterprise Resource Planning (ERP), ERP, ERP software, HR software, NetSuite, NetSuite ERP, Oracle, oracle netsuite, Oracle NetSuite ERP, SME - May 21, 2021Long regarded as the #1 cloud ERP solution, Oracle NetSuite ERP offers a robust portfolio of procedural management software that streamlines business processes for 24,000+ cross-industry customers. The company has experienced great success as both an upgrade from less powerful ERP systems and as a solution that pulls multiple disconnected systems together. Their holistic approach to enterprise management is best illustrated by their seven key feature categories:
- Financial Management
- Financial Planning
- Order Management
- Procurement
- Production Management
- Supply Chain Management
- Warehouse and Fulfillment
The NetSuite ERP portfolio can eliminate a lot of administrative headaches at businesses of any size, but is their ERP the right solution for your business? Take a look at some of the pros and cons that their current customers have highlighted to help you make an informed purchasing decision.
Read Next: Essential Features in Foodservice ERP
A Deep Dive Into Oracle NetSuite ERP
The Pros of Oracle NetSuite ERP
Customizable and Scalable Features
NetSuite offers the same flexibility as most other platforms in the way of add-on modules, user seats, and length of contract. However, Oracle NetSuite’s platform sets itself apart by extending several options to customize their boilerplate solutions to fit your business needs. Users have praised the customizable templates that NetSuite offers in all of its ERP modules, and although doing so may require more extensive technical knowledge, users can code their own solutions into any of the modules.
A favorite customizable feature in Oracle NetSuite ERP can be found in the HR SuitePeople module, where administrators have the freedom to customize and adjust pay options beyond typical pay categories.
Larger companies like Smartsheet have chosen NetSuite because of scalability built into its ready-made ERP features. Mark Mader, the CEO of Smartsheet, specifically highlighted how the SuiteBilling billing and revenue software has enabled his company to grow:
“We needed a solution that could support significant growth in our primary segments—enterprise customers as well as SMBs where we leverage a self-service model—each of which has its own unique set of complexities…NetSuite was the only solution that offered us the ability to automate both the back office and customer-facing aspects across both these important segments of our business.”
Strong Business Intelligence Backbone
NetSuite ERP consistently receives high marks for its business intelligence and financial management tools. Through the platform’s automation of processes like billing, accounting, and reporting, finance teams can focus on financial planning, predictive analysis, and other strategic product and systems-facing actions that require their expertise.
One of their strongest business intelligence and finance features is SuiteBilling, advertised as the industry’s first unified order-to-billing-to-revenue recognition solution on the cloud. Other notable features in this segment of the NetSuite ERP include revenue recognition, customizable analytics and dashboards, and multi-currency transaction capabilities.
Workflow and People Management
At the core of any business, you’ll find people relations and management. Many companies rely on separate HR software that does not wholly integrate with their other company software. But NetSuite ERP’s HR module, SuitePeople, seamlessly connects HR data with financial, procurement, project, payroll, planning, and budgeting data across other modules in the platform. These connections help companies set and analyze performance against company-wide, department, and individual KPIs based on product and market success. NetSuite’s analytics framework is particularly useful for visualizing these types of metrics, as the dashboard shows people and financial analytics side by side and in real-time.
Beyond the people analytics found in NetSuite ERP, you’ll also find a system that simultaneously encourages administrative freedom with widespread employee data protection. Features like the employee directory and other searchable databases within the system make it easy for anyone to connect with the right person in the organization. However, features like effective dating and access control ensure that only administrators with the right access privileges can view employees’ most private data.

The Cons of Oracle NetSuite ERP
Pricing and Add-On Costs
Although some custom packages and pricing options are available, NetSuite’s baseline package costs $999 a month plus $99 per user, which will likely strain the budgets of smaller companies. These costs also don’t account for the fact that companies pay for nearly every customization they choose to add, with things like 24/7 support and upgrading to the latest versions of different modules incurring extra fees.
You’re paying for a high-value product that streamlines all of your business software into one tool. So if the price works for your business, it makes sense to pay a higher price than you might pay for a solution like QuickBooks Enterprise, which includes many financial and BI modules, but completely misses on CRM and HRMS features. The ROI is there for the right business model, budget, and tenacity to keep up with changing costs on the platform.
Customer Support
NetSuite’s technical support is included with all NetSuite subscriptions, but multiple user reviews have indicated the limitations to the service. The included support package offers only 10 hours of customer online support, during regular business hours Monday through Friday. Premium and Advanced Customer Support packages extend that service to 24/7 support for additional fees. Users have also expressed that the support team offers highly technical solutions without always guiding customers, which makes it difficult for teams with less technical staff to resolve NetSuite ERP problems.

Although their actual support team may be limited in the scope of what they offer to customers, NetSuite ERP extends several self-help resources to their customers for free:
- SuiteAnswers support ticketing system
- NetSuite support user group
- Online case submission
- Full training class curriculum
Accessibility for SMEs
Oracle NetSuite has often claimed that they want to be an ERP solution for small and mid-size enterprises (SMEs), but many SMEs have expressed that the solution better fits larger companies. These smaller organizations have shared that the customizations that they want or need to implement in their ERP require two things that they don’t always have: specialized employees who know how to make those coded adjustments, and large budgets to pay for customizations and new add-ons. Managing customizations and version history across the portfolio may require more training, specialized knowledge, FTE, and budget than SMEs can reasonably afford, which is why the solution continues to be selected by mostly larger enterprises.
Read Next: Three Key Advances in ERP for 2021
The post Oracle NetSuite ERP: The Pros and Cons appeared first on CIO Insight.
top2021’s Most Successful Phishing Ploys (So Far)
Posted in: phishing, Security - May 20, 2021Fishing competitions take place all over the world. Anglers attempt all kinds of strategies in their attempts to land the big one. Phishing plays a similar game. Cybercriminals devise and constantly revise their strategies to land their big fish of their own – access to financial data, the ability to lock users out and hold them to ransom, or disrupt societal infrastructure.
The latest ploys are laid out in the Q1 2021 top-clicked phishing report by KnowBe4. Here are the winners of the phishing competition based on email subject lines:
| General Email Subject Line | |
|---|---|
| Password Check Required Immediately | 31% |
| Revised Vacation & Sick Time Policy | 15% |
| COVID-19 Remote Work Policy Update | 13% |
| COVID-19 Vaccine Interest Survey | 10% |
| Important: Dress Code Changes | 7% |
| Scheduled Server Maintenance -- No Internet Access | 6% |
| De-activation of [[email]] in Process | 5% |
| Test of the [[company name]] Emergency Notification System | 5% |
| Scanned image from MX2310U[[domain]] | 4% |
| Recent Activity Report | 4% |
| Source: KnowB4.com |
As you can see, businesses are very much in the crosshairs as they are likely to bear the most fruit in the form of data and personally identifiable information. Predictably, password scams top the list. This makes sense given the insanity of endless passwords for a litany of sites. Once users get comfortable with current rules, it is not uncommon for users to receive a rash of emails from different sites expressing changes to password and security policies. That, in turn, leads to passwords being changed more often, and of course, more characters of growing complexity being added. No wonder this is a big area of user annoyance, disagreement, and frailty. The bad guys are latching onto it.
Think about it for a moment. Your average techie may be enamored by the idea of unbreakable passwords that are impossible to guess. But the average user would rather use a simple password that is easy to remember and is never changed. Regular prodding to change passwords or add more obscure characters has some users up in arms, and others in a state of despair. In such a state of mind, they may lower their guard and click on something malicious, thinking it to be just the latest meddlesome interference from IT. It is up to IT to ensure their actions and password enforcements don’t antagonize users and force them into that frame of mind. Otherwise, IT will continue to be overworked by phishing flaps.
Read more: Check out eSecurity Planet’s comparison of top password managers in Dashlane vs. 1Password and Dashlane vs. LastPass
“The bad guys go with what works and in Q1, nearly a third of the users who fell for a phishing email clicked on one related to a password check,” said Stu Sjouwerman, CEO, KnowBe4. “Always check with your IT department through a known good phone number, email address or internal system before clicking on an email related to checking or changing a password because it only takes one wrong click to cause monumental damage.”
Further targets for cybercriminals include HR traffic. HR departments have been busy during the pandemic. Many attempted to make up for lack of onsite presence by sending far more email traffic than before. Hackers have realized this and have achieved phishing success with subject lines about vacation and sick time, remote work policy changes, vaccine information, and dress codes. If HR traffic is high, a phishing attempt posing as an email from HR may strike gold.
IT department traffic is another area of phishing success. With so much remote work being done, IT departments have been forced to be more vocal than before. The bad guys are tapping into this area with subject areas about server downtime, email account deactivation, and various tests being conducted. Scanned images and package delivery notifications are further sources of phishing success, as are social media messages – LinkedIn phishing messages dominate in social media email subjects.
The motto is clear: Think Before You Click.
The post 2021’s Most Successful Phishing Ploys (So Far) appeared first on CIO Insight.
topDaman News and Events
This showcases our company news and upcoming events. Please check back as this page will change frequently.


